Everyone can agree that packaging and creating a Windows app is a daunting task.
In this blog, we will show you step-by-step how to package and deploy a Win32 app in Microsoft Intune and how to do this in a smart way just in a couple of clicks.
What is a win32 app?
Win32 applications are programs written for the Windows operating system. Microsoft Intune allows Win32 app management capabilities and supports both 32-bit and 64-bit operating system architecture for Windows applications. Win32 app management allows you to manage different types of files, such as .msi, .exe, .msix or any other formats. The only thing you must remember before creating a win32 app in Microsoft Intune I have to package it.
Intune Win32 App Deployment Prerequisites
To be able to manage win32 apps in Microsoft Intune, you should meet some criteria:
- Use Windows 10 version 1607 or later (Enterprise, Pro, or Education editions).
- Devices must be enrolled in Intune and either:
- Azure AD joined
- Hybrid Azure AD joined
- Windows application size must not be greater than 8 GB per app.
Process of Intune Win32 App Deployment
Step 0. Download Microsoft Win32 Content Prep Tool
As we already mentioned, before you can upload a win32 app to Microsoft Intune, you must package it by using the Microsoft Win32 Content Prep Tool. The tool converts installation files into an .intunewin format. Also, it detects some of the parameters that Intune requires to determine the application installation state. You can download Microsoft Win32 Content Prep Tool on GitHub.
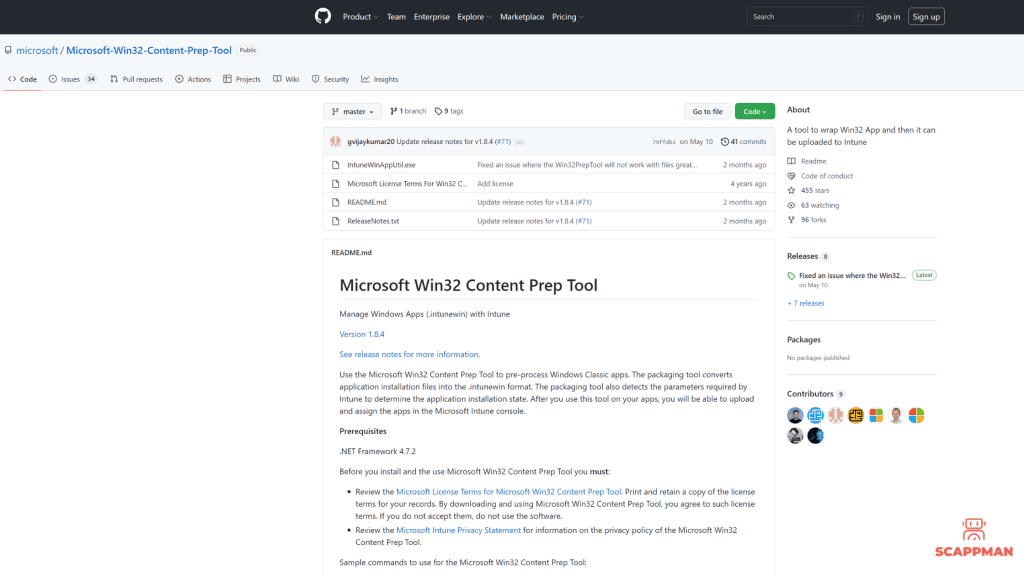
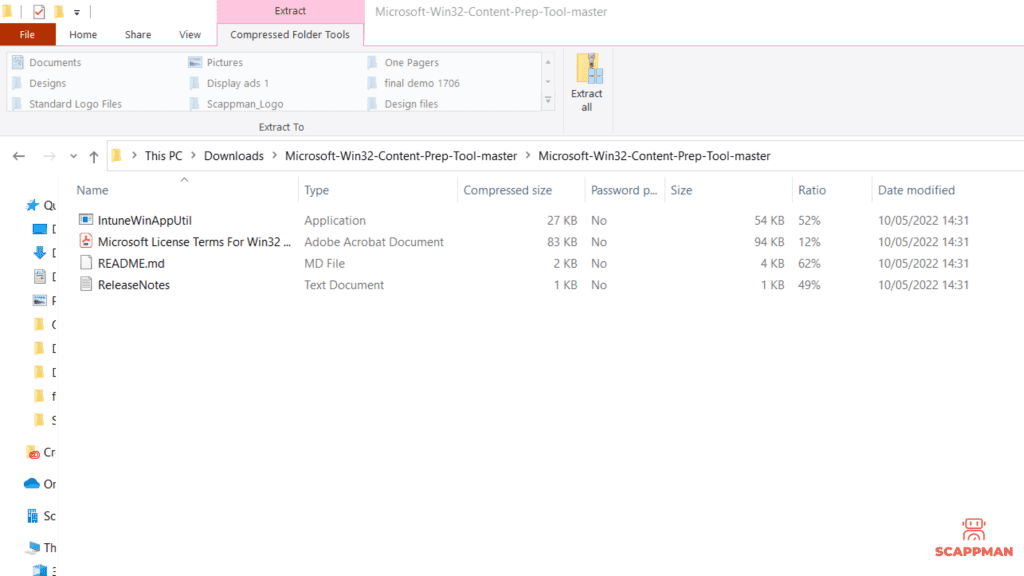
When you download Intune Win32 Content Prep tool, it’s a .zip file and you must extract the contents to a folder. The .zip file contains IntuneWinAppUtil.exe, Microsoft License Terms, Read me file and Release notes.
Use the latest version of the Microsoft Win32 Content Prep Tool otherwise, you’ll see a warning that says the app was packaged using an older version of the tool.
Step 1. Win32 app preparation
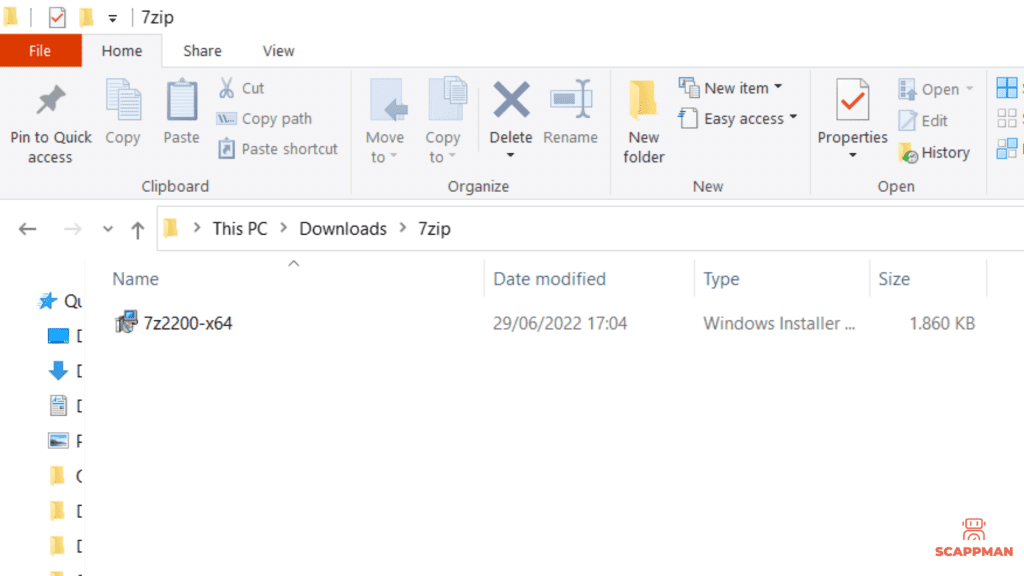
In this step, we’re going to package an application – wrap it into an .intunewin using Intune Win32 Content Prep tool. As an example, we will use 7zip. Make sure, that your installation file is in a specific folder, and that you know the folder’s name.
Step 2. Packaging a Win32 app in Intune (.intunewin)
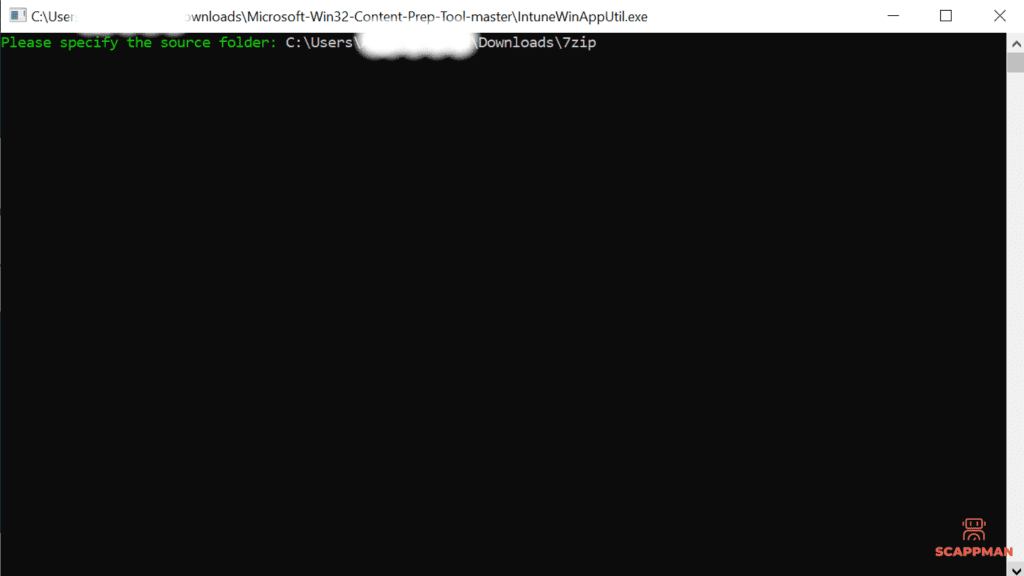
It’s time for packaging! Open the IntuneWinAppUtil.exe and provide the folder of the installation file – in this case, the location of the 7zip installation file (7z2200-x64).
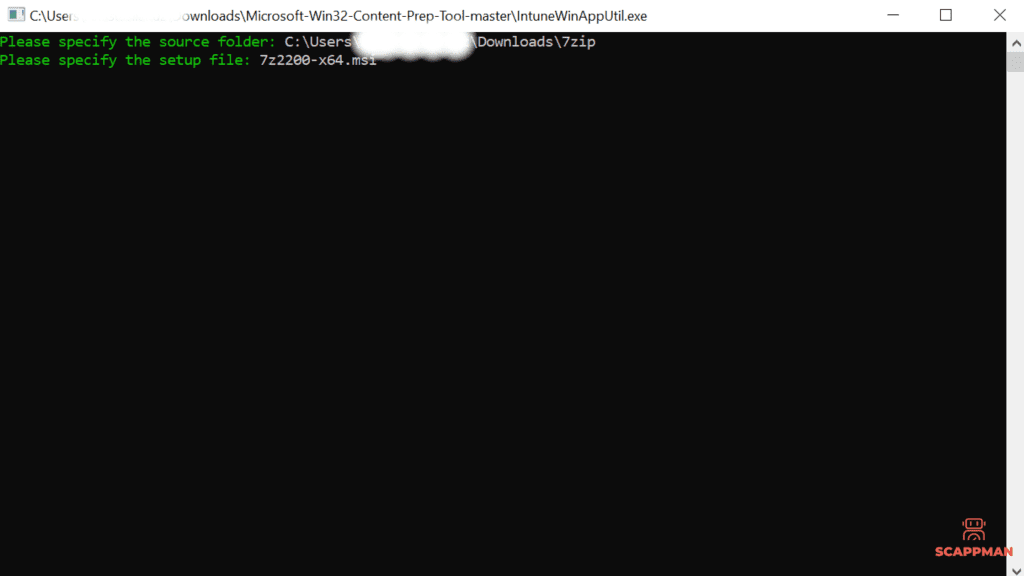
Then specify the file that you’re going to package.
And, finally, specify the output folder.
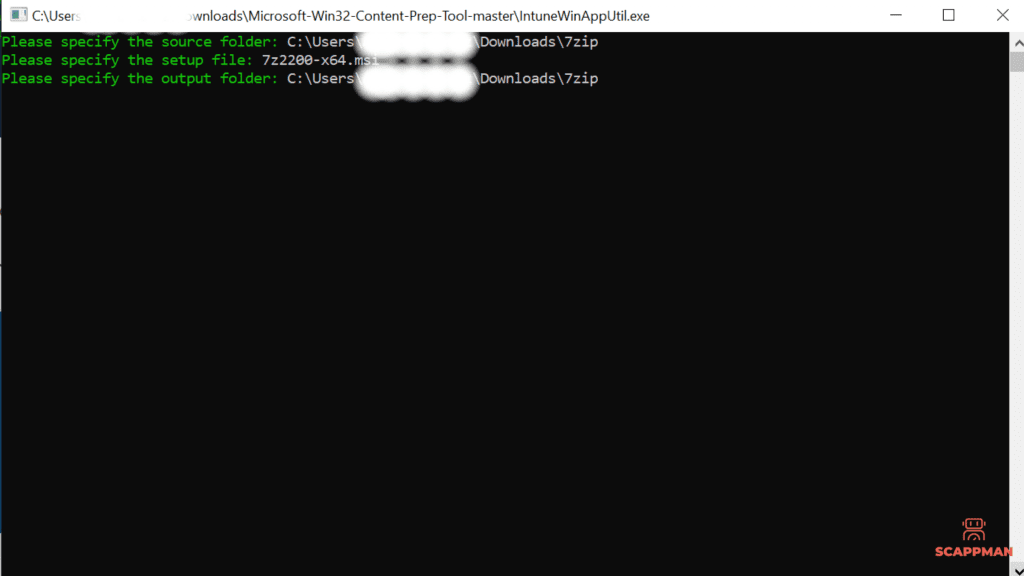
Press Enter, and voila – the .intunewin file is ready.
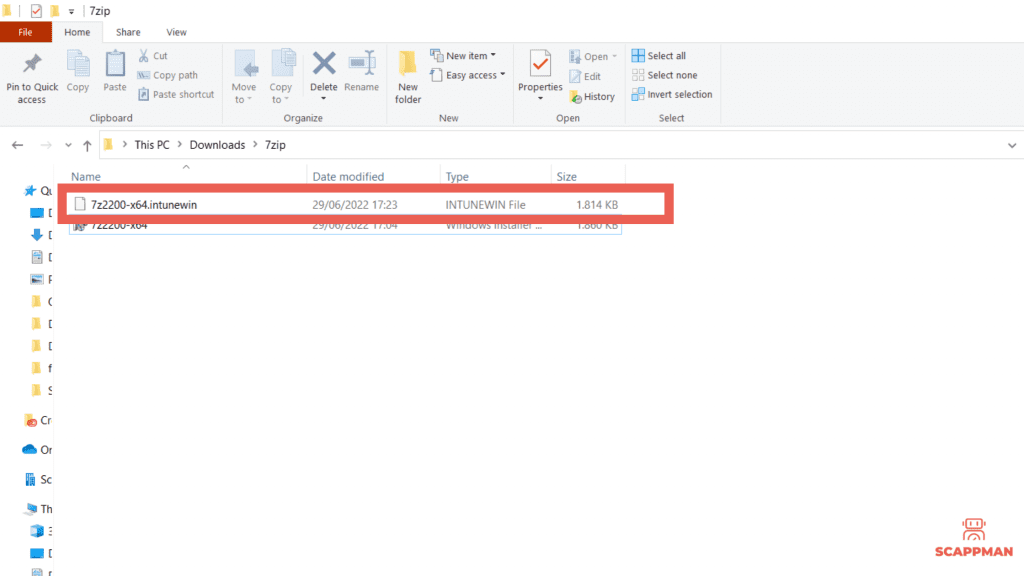
Once you have an application with the .intunewin format, you can create that win32 application in Intune.
Step 3. Intune Win32 App Deployment
Finally, we’re about to start Win32 app deployment in Microsoft Intune. For the following steps log in to Microsoft Endpoint Manager admin center.
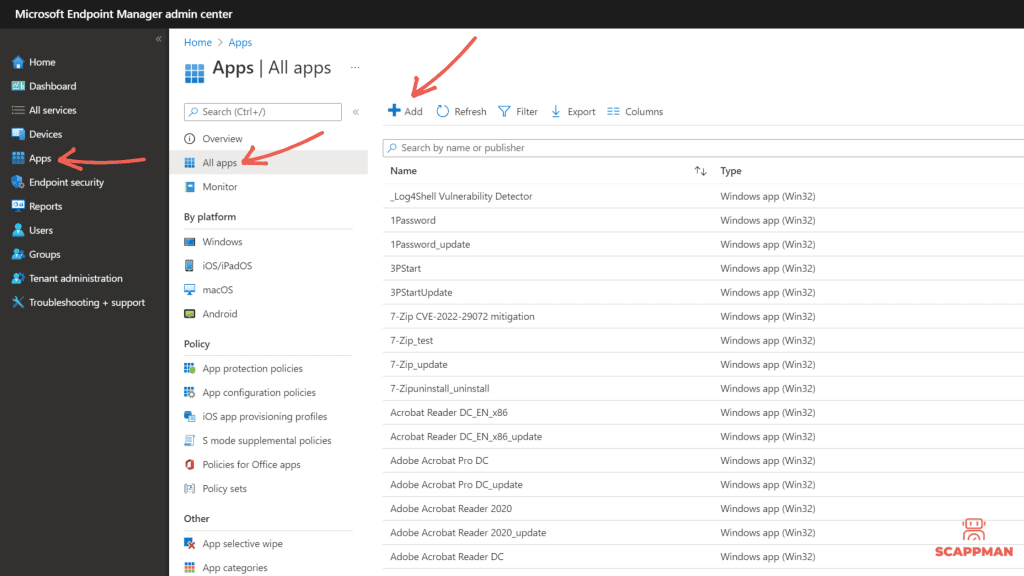
Navigate to Apps > All apps and press +App.
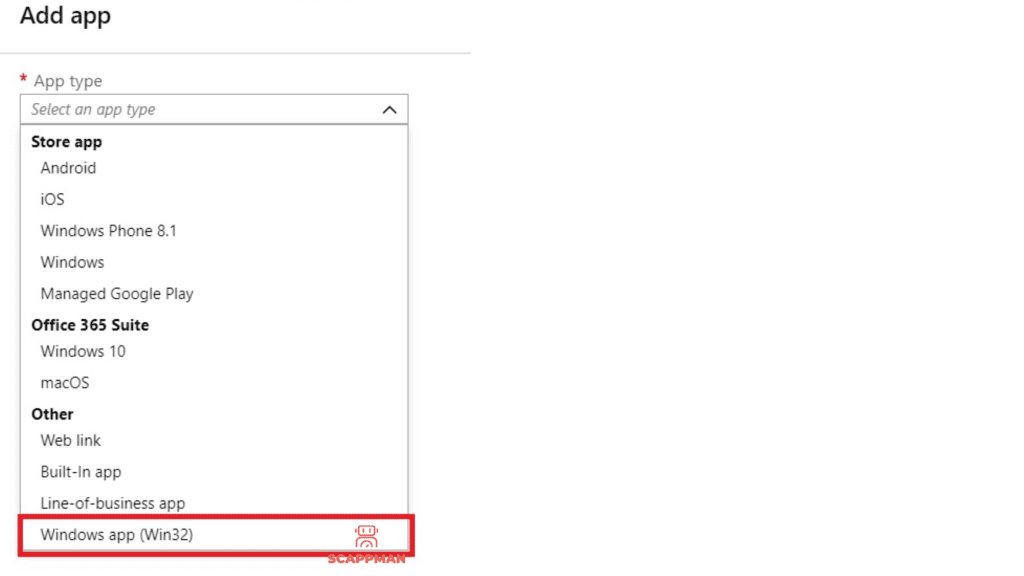
In the App type select Other – Windows app (Win32).
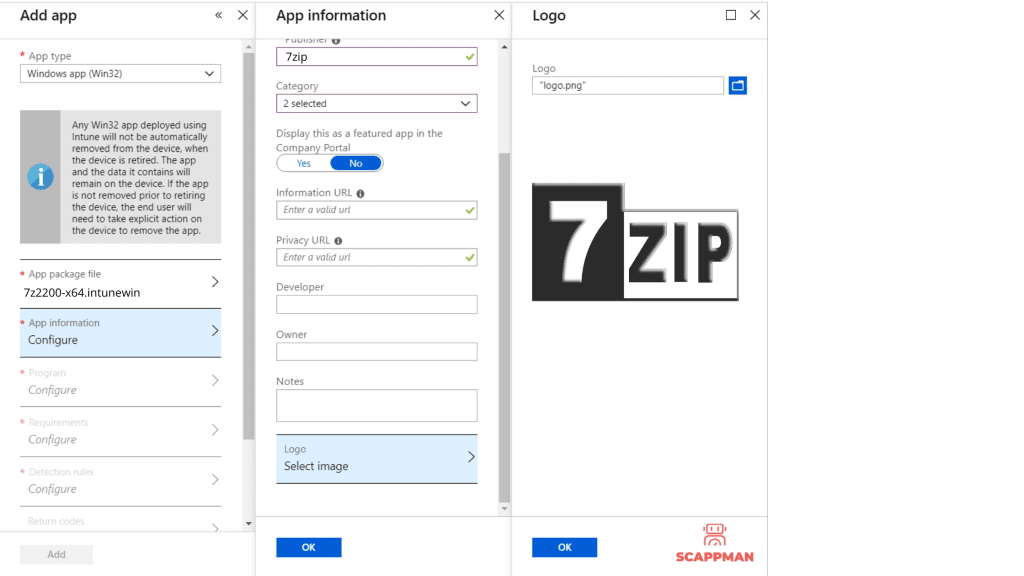
Open the App package file blade and browse for the just created 7z2200-x64.intunewin. The next step is to fill in some application information like Name, Description, Publisher, Category, Information URL, Privacy URL, Developer, Owner, Notes and upload an app’s logo. This icon is displayed with the app when users browse through the Company portal.
In the Program section, you can configure the application installation process using commands, install and device restart behavior.
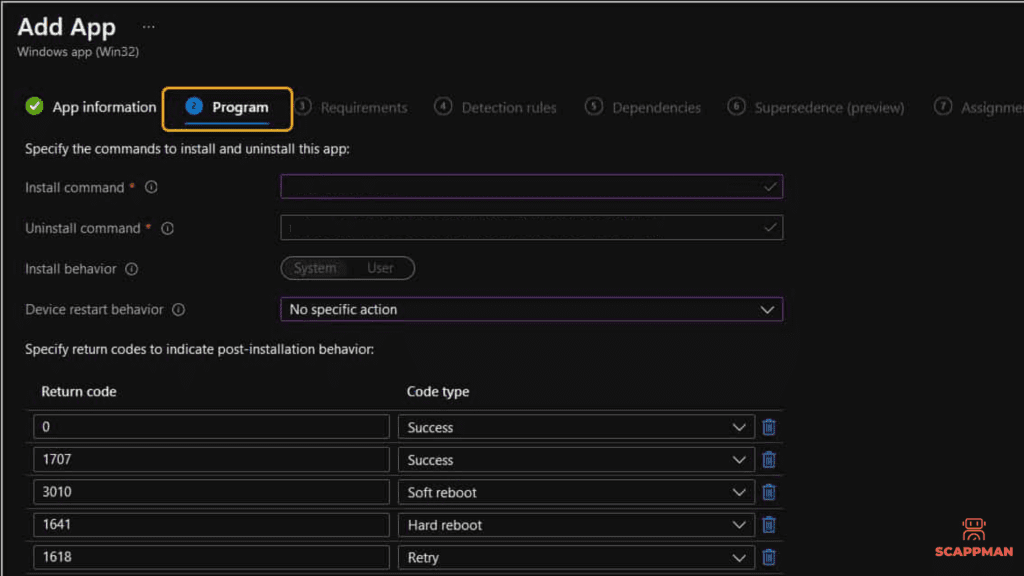
Install command – normally, it’s filled in automatically. If it’s not the case – customize the app installation process.
Uninstall command – msiexec /x “{12345A67-89B0-1234-5678-000001000000}”
Device restart behavior – here you can select one of 4 options:
- Determine behavior based on return codes
- No specific action: Choose this option to suppress device restarts during the app installation of MSI-based apps. This is preferred if you don’t want to reboot the device after the app installation
- App install may force a device to restart
- Intune will force a mandatory device restart
Also, you can specify return codes to indicate post-installation behavior. Return code entries are added by default during app creation. But you can add more return codes or change existing ones. Code types:
- Success – the return code was successfully installed
- Retry – the return code will be attempted to be installed the application 3 times. It will wait 5 minutes between each attempt.
- Soft reboot allows the private app to be installed without a reboot. However, reboot is necessary to complete application installation.
- Hard reboot does not allow the application to be installed on the device without a reboot
- Failed – the application is failed to be installed
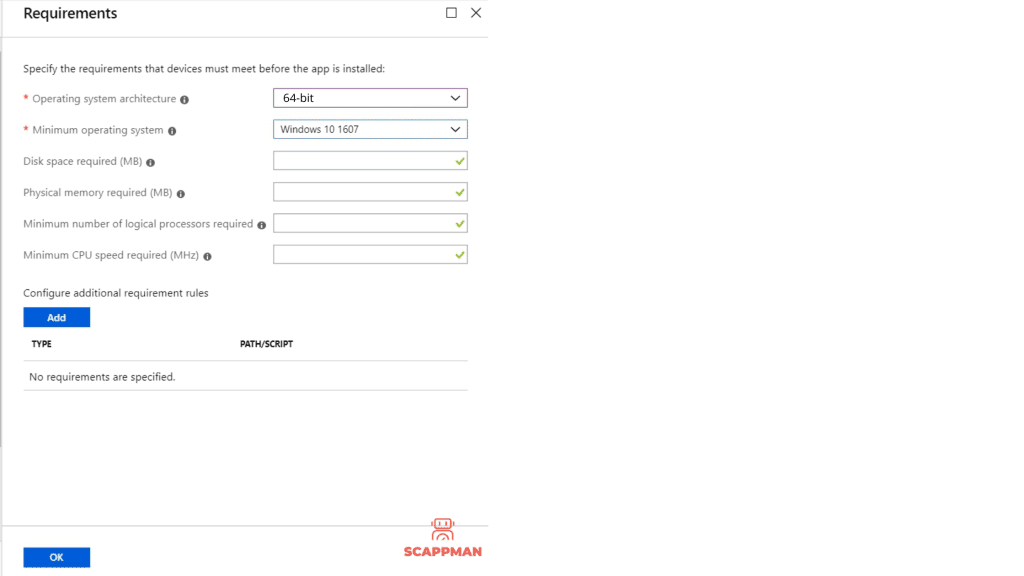
In the Requirements you can fill in the requirements that devices must meet to install the app:
- Operating system architecture: 32-bit / 64-bit
- Minimum operating system
- Disk space required (optional)
- Physical memory required (optional)
- Minimum number of logical processors required (optional)
- Minimum CPU speed required (optional)
- You can add additional requirements.
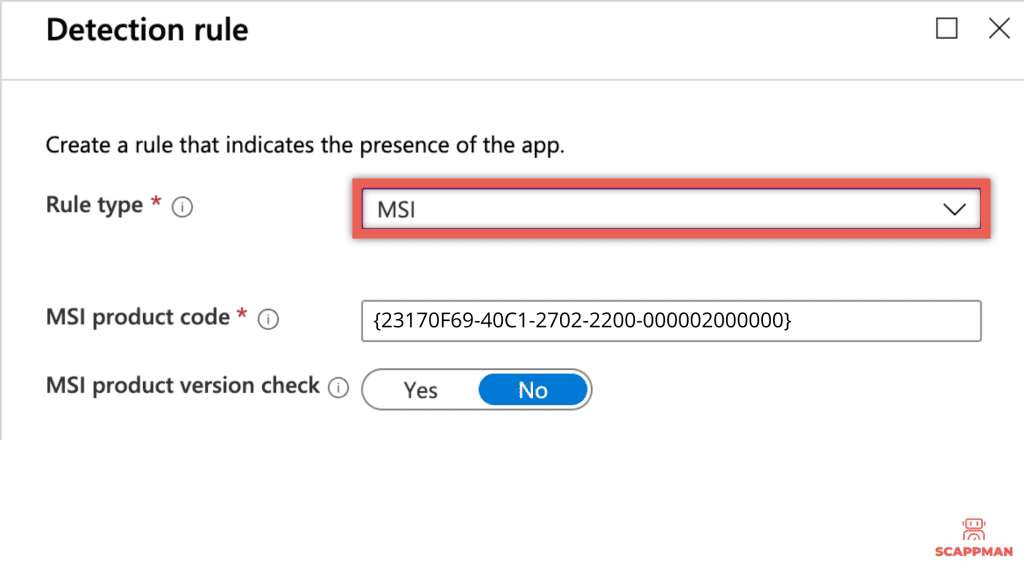
When deploying the win32 app in Microsoft Intune you must specify the detection rules – how the availability of the application will be detected. It can be done manually or by using a custom PowerShell script.
Manual detection rules format
- MSI: this rule type enables the admin to create a detection rule that must detect a specific MSI product code or even a specific MSI version. This detection rule type can only be used once.
- File rule type enables the admin to create a detection rule that detects a specific file or folder, date, version, or size to determine the installation of the private app. Requirement rules:
– Path – specify the full path of the folder that contains the application file
– File or folder – specify the file or folder that should be used to detect the app
– Detection method – choose the option that should be used to detect the installation of the app (File or folder exists, Date modified, Date created, String (version), Size in MB)
- Registry: with this detection rule the Intune admin enables detection of the application installation based on the value, string, integer, or version. Requirement rules:
– Key path – identify the full path of the registry entry containing the value that should be used to detect the installation of the app. Ex.: HKEY_LOCAL_MACHINE\Software\7zip
– Value name: if this property is empty, the detection will happen on the default value. The default value will also be used as a detection value if the detection method is other than file or folder existence.
– Detection method: there are 5 self-explaining methods – Key exists, Key does not exist, String comparison, Version comparison, integer comparison
In our example, we’re going to use the MSI detection rule. The MSI product code is populated automatically, however, if you don’t see it, add it manually.
Custom PowerShell Script: That rule format enables the Intune admin to create detection rules that can check on basically anything that can be scripted, as long as the script has the correct output. It requires the configuration properties as mentioned below:
- Script file – select a PowerShell script that will be used to detect the installation of the application. When the script exit code is 0 and STDOUT contains any data, the app is detected.
- Run the script as a 32-bit process on 64-bit clients
- Enforce script signature check – Select Yes to verify that a trusted publisher has signed the script, which will allow the script to run with no warnings or prompts displayed. The script will run unblocked. Select No (default) to run the script with user confirmation without signature verification.
Intune checks the results from the running script. It reads the values written by the script to the STDOUT stream, the standard error (STDERR) stream, and the exit code. If the script exits with a nonzero value, the script fails, and the application is not installed. If the exit code is zero and STDOUT has data, the application is installed.
While uploading the win32 app to Microsoft Intune you can add dependencies – applications, that must be installed before your win32 app.
In the Assignments menu, you can configure Required, Available for enrolled devices, or Uninstall group assignments for the win32 app. And, finally, after reviewing all the configurations you can add your win32 application to Microsoft Intune.
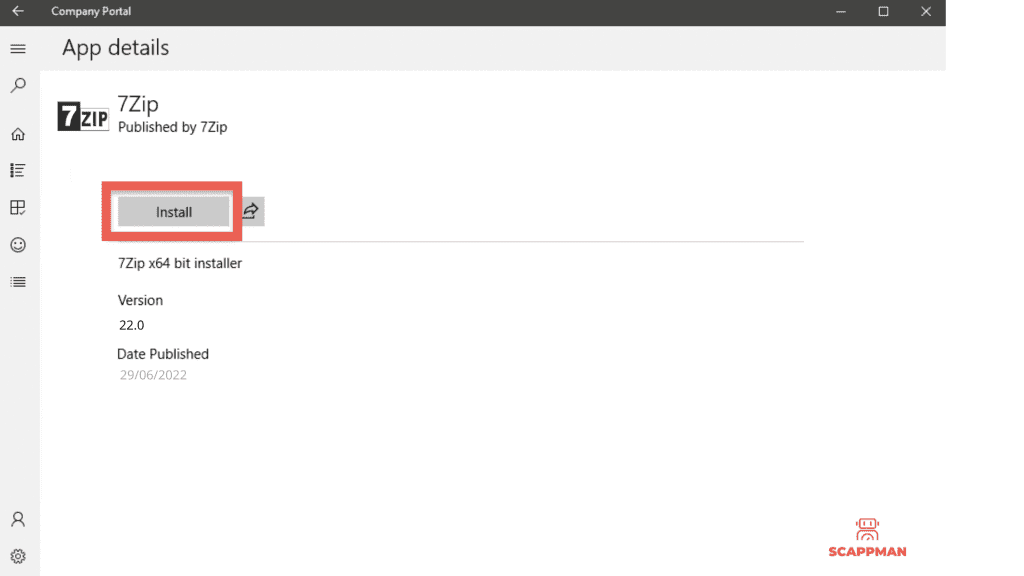
Once the application is uploaded, the assigned user will see Windows notifications for the required and available app installations. The applications will become available on the Company Portal.
Quick and easy way to create and deploy Win32 applications in Microsoft Intune
We’ve just discussed the process of creation and deployment of win32 in Microsoft Intune. Quite a long and complex process, huh? You must go over this process again and again when you’re creating apps for your organization or clients. If you want to update those applications – the same story. Manually packaging and then creating third-party applications like 7zip, Adobe Acrobat Reader and Google Chrome in Microsoft Intune take a lot of your valuable time.
What if you could automate third-party application installations and updates in Microsoft Intune? Scappman can do this for you ?.
With Scappman you can automate the whole process of application management in Microsoft Intune.
To create a third-party application in your Intune environment with Scappman you just must choose the application from the wide selection of the Scappman App store (we have more than 800 public applications available!) and hit install.
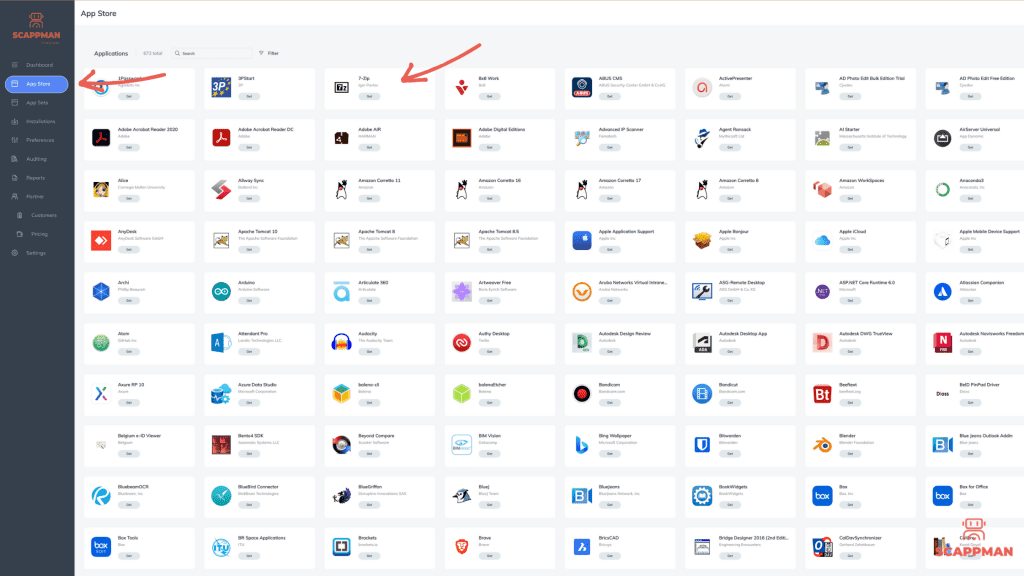
With Scappman, the packaging and win32 application creation process in Intune looks like this:
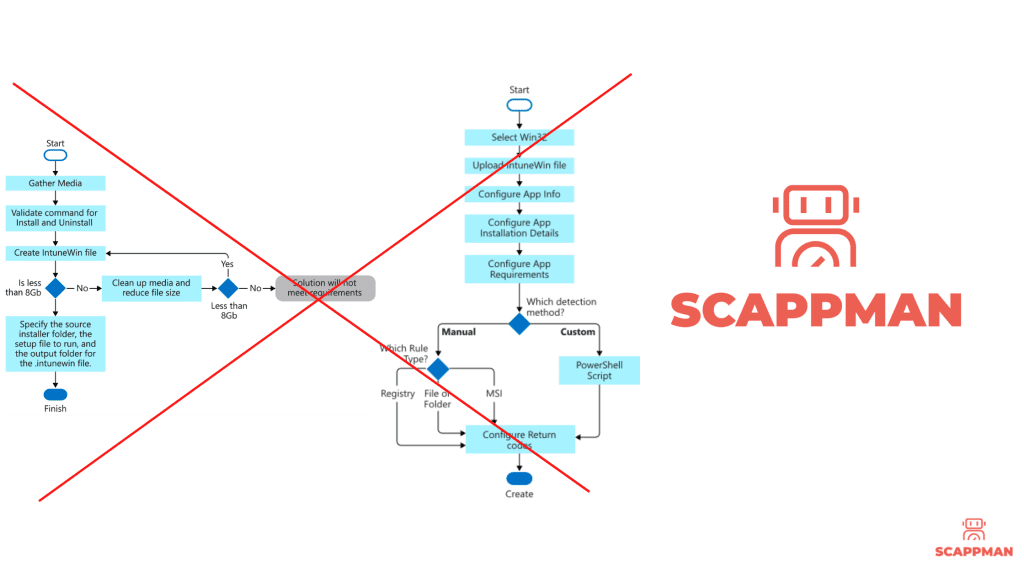
Just imagine how much time you can save.
To know more about how you can create and manage third-party applications in Microsoft Intune with Scappman watch the demo.
P.S. Deploying applications with Scappman gives you a lot of freedom to configure the installation/post-installation process of the application, so in the next blogs, we’ll show the logic Scappman has behind the application installation process.