Vulnerability management is an important part of any organization’s cybersecurity strategy. It helps to identify, assess, and mitigate risks associated with vulnerabilities in software and hardware. Microsoft has a comprehensive vulnerability management solution that helps companies protect against a variety of threats. Threat & Vulnerability Management (TVM) is a built-in capability in Microsoft Defender that follows a risk-based approach to discover, prioritize, and remediate endpoint vulnerabilities and misconfigurations. Microsoft has been working on improving their vulnerability management system for years now and recently they released a new Vulnerability management solution for a public review.
Microsoft Defender Vulnerability Management: overview
Microsoft has announced a public review of Microsoft Defender Vulnerability Management service, a single solution that offers the full set of Microsoft’s vulnerability management capabilities to help companies mitigate vulnerabilities more easily.
The core version of Vulnerability Management tools was released in 2019 as Threat and Vulnerability Management – a built-in capability in Microsoft Defender Advanced Threat Protection. Since then, Microsoft has been constantly working on the tool to provide even better experience in monitoring, managing and mitigating vulnerabilities.
Read more about Microsoft TVM and its functionality in our blog Detecting vulnerable applications with Microsoft Threat and Vulnerability Management.
Besides all the existing threat & vulnerability management functionality currently available, a new service will provide asset inventories, smart assessment, and built-in remediation tools for Windows, macOS, Linux, Android, iOS, and network devices.
Defender Vulnerability Management service will also include more advanced capabilities:
- Security baseline assessments – creating customizable baseline profiles to measure risk compliance against established benchmarks, such as, Center for Internet Security (CIS) and Security Technical Implementation Guides (STIG).
- Browser extension assessments – View a list of the browser extensions installed across different browsers in your organization.
- Digital certificate assessments – View a list of certificates installed across your organization in a single central certificate inventory page.
- Network shares analysis – See actionable security recommendations, in the security recommendations page, for network share configurations identified as vulnerable.
- Blocking vulnerable applications (beta)
- Vulnerability assessment for unmanaged endpoints (soon)
Microsoft Defender Vulnerability Management will be available in public preview as a standalone and as an add-on for Microsoft Defender for Endpoint Plan 2 customers.
Companies wanting to try the public previews of Microsoft Defender Vulnerability Management -both as a “standalone” service and as an add-on to Microsoft Defender for Endpoint Plan 2 – must request the free 120-day public preview here.
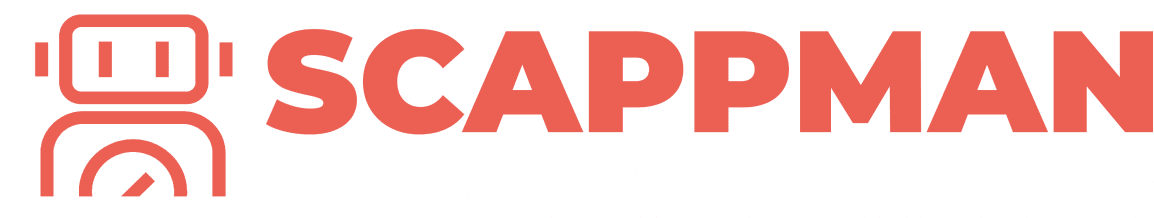
Security baseline assessment
With the new release, you will be able to continuously monitor the security posture of your endpoints and measure and compare risk compliance with industry benchmarks – CIS and STIG in real-time. Additional benchmarks will be available soon.
To use this functionality, you must create a Baseline profile. Go to Vulnerability management > Baselines assessment. Select the Profiles tab at the top, then select the Create profile button. Enter a name and description for your security baselines profile and select Next. On the Baseline profile scope page set the profile settings such as software, base benchmark (CIS or STIG), and the compliance level and select Next. Finally, select the configurations you want to include in the profile.
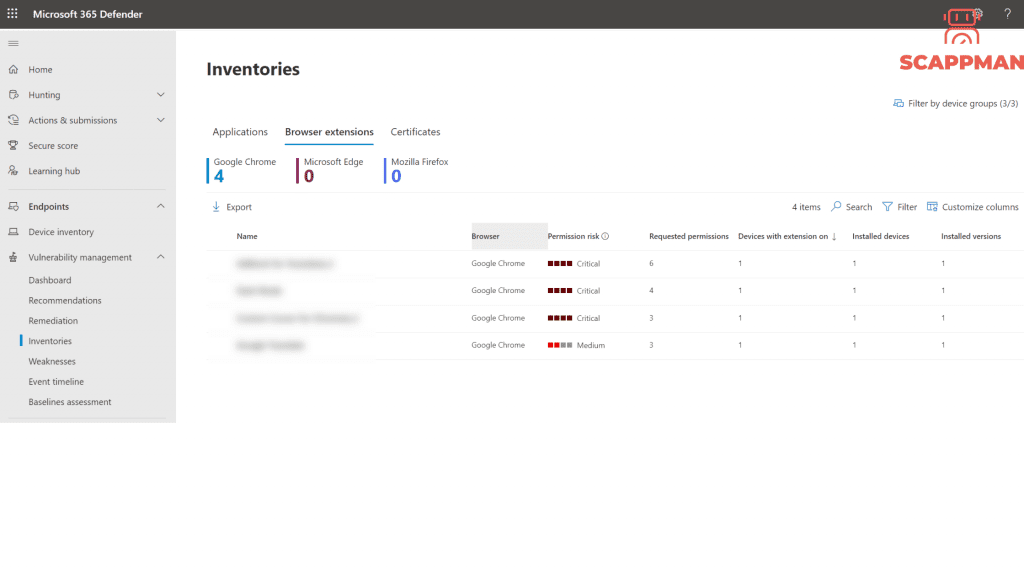
Browser extension inventory
From now on you can monitor web browser extensions installed on your endpoints. Defender Vulnerability Management provides detailed information on the risk level of the installed browser extensions, so you can make informed decisions on managing extensions in the organization’s environment.
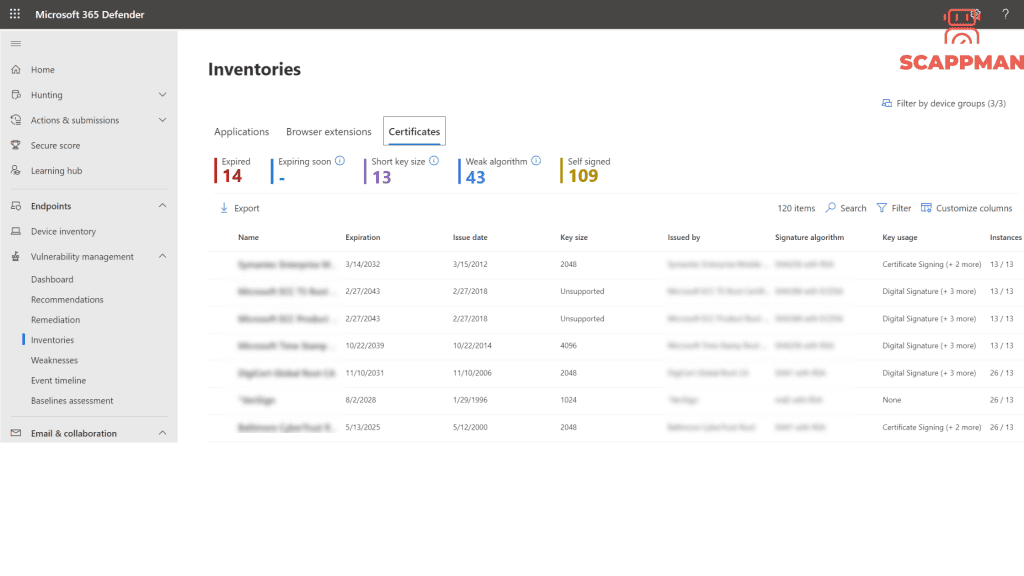
Digital certificate inventory
Digital certificates help provide privacy, security, and authentication to transfer data within your network and over the Internet. Expired certificates could expose vulnerabilities within your company, disrupt service, or cause downtimes.
The certificate inventory makes it easy to manage certificates from one place. You can:
- Identify certificates that are about to expire
- ensure compliance with the company’s policies
- detect potential vulnerabilities if weak signature algorithms, short key size or weak signature hash algorithms are used.
To view your certificates, go to Vulnerability management > Software inventory and select the Certificates tab.
Network shares analysis
Companies use internal network shares to send data and to provide access to files and documents. To prevent attackers from stealing data from your organization Microsoft created new configuration assessments that identify the common weaknesses that expose your endpoints to attack vectors in Windows network shares.
The following recommendations will be available as part of the new assessments:
- Disallow offline access to shares
- Remove shares from the root folder
- Remove share write permission set to ‘Everyone’
- Set folder enumeration for shares